
- Jul 31, 2025
Is 3-Tiers Architecture Justified?
In fintech, security isn’t optional—it’s mandatory. With sensitive data at stake and tight central bank regulations, architecture must prioritize containment. That’s where three-tier architecture earns its place.
What Is Three-Tier Architecture?
It divides your infrastructure into three isolated zones, often mapped to separate VLANs:
Public Zone: Exposed to the internet. Hosts web frontends, mobile entry points, and API gateways. This is where threats land first.
Application Zone: Hosts backend services and middleware. Serves as a buffer—validates, authenticates, and processes requests.
Data Zone: Home to databases, core banking systems, and other critical resources. Access is tightly controlled.
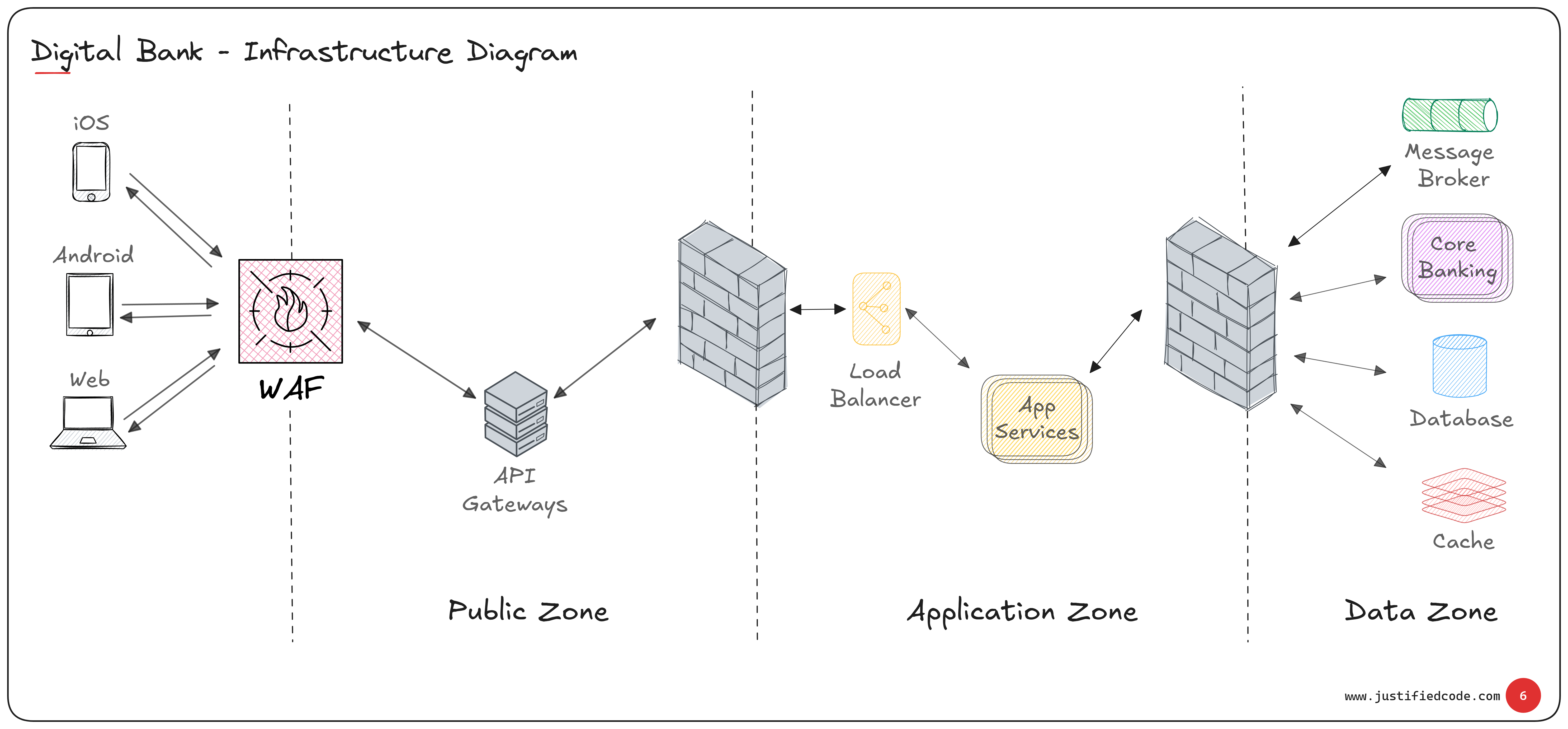
You see from the diagram above, no direct access is allowed between Public and Data zones. All traffic must flow through the Application zone, where strict rules apply.
Why Isolation Is Critical
In real-world fintech deployments, attackers don’t knock—they sneak in.
A server in the Public zone might be compromised through an unpatched Linux or Windows vulnerability. Or maybe an insider is silently siphoning data for months. Either way, segregating access at the network level stops the breach from spreading.
Even if an attacker gets command-line access in the Public zone, they can’t ping or connect to the Data zone. That’s the design. No telnet. No database ports. No exceptions.
We assume the attacker can bypass the WAF and app-level checks. That’s not paranoia—it’s reality. Which is why network-level segmentation is your final safety net.
The Role of WAFs: F5, Citrix, Barracuda
WAFs are your first line of defense. F5 is powerful but pricey. Citrix is mid-range. Barracuda is affordable.
They’re great at blocking known attacks, but attackers evolve fast. You cannot rely solely on WAFs. Design like they’ll fail.
Even the best WAF can’t replace the need for network isolation and tiered defense.
Use an API Gateway—Don’t Build One
Instead of building your own gateway logic, use a proven tool like tyk.io or Kong API Gateway. It sits in the Public zone and gives you:
Rate limiting
Authentication (e.g., JWT validation)
Protocol translation (e.g., REST to gRPC)
Caching and logging
Some Bank officers still rely on SOAP for server to server communications because it supports message-level encryption. If that’s the case, make sure you choose a gateway that supports soap or has a plugin for that.
You configure these features. You don’t code them. That’s leverage.
Real-World Application Zone Setup
In practice, your Application zone may include:
Retail services for individual customers
Corporate services for business accounts
-
Middleware that routes:
/internal/* to core banking.
/external/* to credit card networks or third-party services
Only the Application zone talks to the Data zone. And it does so with tight firewall rules, service-level authentication, and limited protocol access.
The Trade-Off
Yes, three-tier architecture adds complexity:
More firewalls
More configuration
More deployment steps
But it contains breaches, and satisfies regulatory requirements.
When security is non-negotiable, this architecture is not overkill—it’s your baseline.
Conclusion
In fintech, assume compromise. Then design for containment.
Three-tier architecture is about survival. And if you’ve seen what can happen when internal services are exposed, you’ll know: the cost of not doing this is far higher.
So yes—three-tier architecture is justified. And in many environments, it’s the only responsible choice.
Related Materials
Get exclusive deep dives, private notes, behind-the-scenes thinking, and raw experience from the field. Access Elite Secrets to Build Your Competitive Edge.
If you're designing systems like the ones discussed here, this toolbox might help.
- Free email delivery